Why we made up our own minds about Zoom
With the recent surge in popularity of tools that support remote working, many of us have, no doubt, come across news articles that address security concerns about Zoom. There are both favourable and unfavourable articles by reputable security industry leaders. Given that this is a tool we use at Equal Experts, we did a thorough analysis and thought that others might be interested in our view.
Our opinion of Zoom is informed first and foremost by our threat model. This is unique to Equal Experts and is based on the threats and risks we are most concerned about. We would caution against using our perspective for other use cases because we almost certainly have different concerns than other organisations and individuals. We make decisions based not just on evidence but on the application of that evidence to our context.
While we deeply value the insights shared by industry experts, we urge all organisations to perform their own threat modelling and risk assessments. No expert, no matter how qualified in their field, should issue universal instructions to “abandon the platform” or “stop using Zoom” without first understanding how the issues affect your specific circumstances.
Empathy and context
Some aspects of Equal Experts that I personally value are our ability to empathise and our use of the prime directive in retrospectives and post-incident reviews. To help put ourselves in their shoes, I’d encourage reading the recent blog post by the CEO of Zoom. This shares their perspective on where they began as a company (and a product), where they are today, and how they plan to address some of the recent issues.
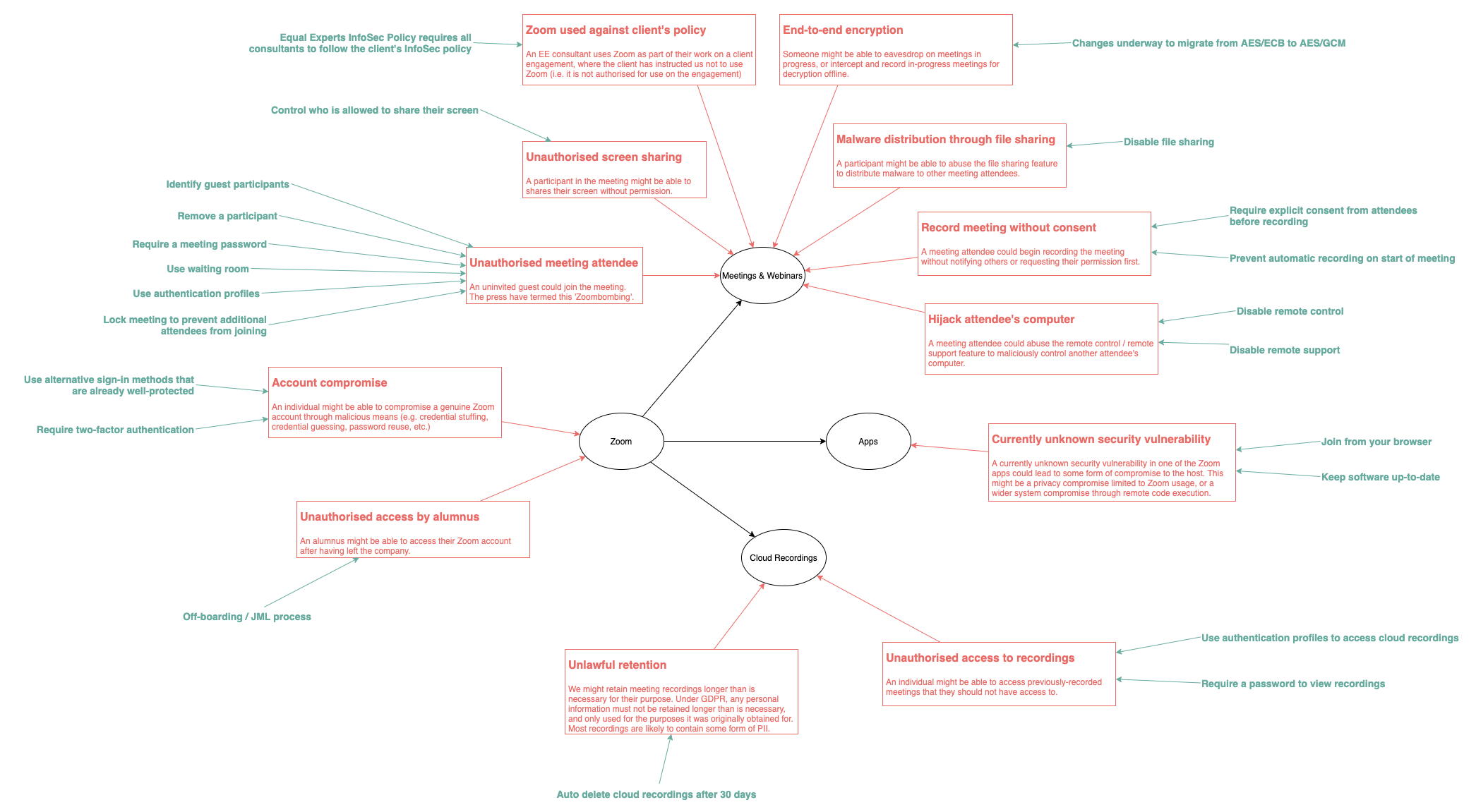
Concerns and issues
Security vulnerabilities
A number of Zoom security-related issues have circulated in the media recently. I’ve highlighted the more widely-discussed issues here. To my knowledge, all of these issues have been fixed, so the only action you should take at the moment is to ensure you’re running the latest version of Zoom, which is considered good security practice for all software.
Anyone particularly concerned about the use of Zoom apps should consider using the “Join from browser” option, which can be enabled by default on all meetings. Alternatively, iOS apps may be better protected due to the sandboxing within the operating system and the additional review required to install the app via the App Store.
ZoomOpener’s unintended video disclosure
In previous versions of Zoom, video was enabled by default when joining a meeting (CVE-2019-13450). This created a situation where people could be tricked (e.g. via phishing) to join a meeting, and their webcam would be enabled automatically. Although users were able to turn this setting off, this was not the default setting and, therefore, could negatively impact user privacy. This was exacerbated by an undocumented local web server included with Zoom (known as the ZoomOpener) that was designed to reduce friction for meeting joiners in Safari on macOS. This web server contained a vulnerability that allowed any website to launch a Zoom meeting when visited.
Note that the use of a local web server is not unique to Zoom. Neither is the fact that it was an undocumented feature:
- BlueJeans (a competitor to Zoom) has adopted the exact same solution to the exact same problem. However, their solution is documented and has not suffered the same security issues.
- JetBrains (a very popular developer tool company) had similar security issues with their own undocumented internal web server within their IDEs, where a “cross-site request forgery (CSRF) flaw in the IDE’s built-in webserver allowed an attacker to access local file system from a malicious web page without user consent”
ZoomOpener remote code execution
When uninstalling Zoom on macOS, the ZoomOpener background process was not also uninstalled (CVE-2019-13567). This created a situation where malicious software could be downloaded onto the user’s computer. Apple issued a silent update to automatically remove ZoomOpener, although this was also addressed in an update to Zoom itself.
Facebook data-sharing on iOS
The Zoom iOS app was discovered to be sending some data to Facebook, even for non-Facebook users. The app has since been updated (v4.6.9) to remove the Facebook SDK and require Facebook users to log in via the browser.
Privacy
Attention tracking
This feature was removed on 1 April.
Meeting recording without consent
A few articles raise concerns about the privacy implications of video recording within Zoom, particularly the ability to record a Zoom meeting without explicit consent from those in the meeting. While the Zoom client does provide a visual indicator that recording is taking place, it’s easy for attendees not to notice this.
Zoom does provide the ability to request consent from attendees before recording can begin, although this is disabled by default.
Cloud recording storage and sharing
Meetings can be recorded locally and in the cloud. While Zoom does provide security controls around sharing within their cloud storage, it is still possible for individuals to inappropriately share downloaded or locally recorded content.
There are numerous configuration options available within Zoom to manage the risk associated with recording and sharing meetings. This includes recording retention periods, access controls and sharing controls, among others.
Insecure default settings
Like any piece of complex software, Zoom has many configuration settings. And like many products, the defaults tend to favour feature adoption over security and privacy. For example, Facebook posts were public by default from 2009 until 2014, when it changed to friends only.
Individuals can generally override these defaults for both their profile and individual meetings if they wish. Some defaults can be locked at an account level, preventing individual users from overriding them. We prefer to use this sparingly. Only where we believe a setting is critical to the security of Equal Experts as well as our employees, associates and clients will we globally configure particular settings without the ability to override them.
Zoombombing
Zoombombing (coined after photobombing) is when an uninvited guest is able to join your meeting without your permission. Unfortunately, the impact of Zoombombing has been quite significant, including the sharing of pornographic and racist material to participants – which is particularly concerning given the popularity of Zoom as a means for schoolchildren to keep in touch with their classmates while they’re stuck at home.
While many of us will remember this headline from the 2014 Commonwealth Games, I assure you that Zoombombing is not the same as the Queen dropping into your photo! For those affected, it is simply not funny.
Zoombombing is not a bug or a vulnerability in Zoom. If you provide any information or service on the internet without authentication, you must assume someone will find it and abuse it. A similar example of this problem is unsecured S3 buckets.
Zoom provides many different ways to host meetings, not all of which require authentication. In fact, I’m confident that we would not have selected it for use at Equal Experts if all meetings required some form of authentication. While it’s possible to schedule a meeting without requiring attendees to log in, there are also numerous options to prevent uninvited guests from joining your meetings and webinars.
We do not believe it requires a global configuration to require meeting passwords in all cases. We trust that everyone will make wise decisions regarding the use of meeting passwords when appropriate. Zoom has provided advice specifically around this issue.
File sharing
Zoom provides the ability for meeting participants to share files during a meeting. This feature has been abused in conjunction with Zoombombing to deliver malware to meeting participants. This can be disabled if the feature isn’t required.
Screen sharing
Screen sharing is enabled by default for meeting hosts and participants. This is likely to be useful for the majority of our meetings, so we have no intention of preventing it. If you are hosting a public meeting – for example, a remote ExpertTalks meetup over Zoom – we strongly recommend you change this setting to allow host-only screen sharing.
End-to-end encryption
There have been recent articles about Zoom’s use of the term “end-to-end encryption” and how it differs from conventional use. In response, Zoom has published a blog post explaining how encryption is used within their service based on a variety of use cases. There has since been another article from The Intercept with new information, and a follow-up blog post from Zoom promises more information on their encryption design in the coming days.
Access control
Zoom provides a variety of different authentication methods to suit your use case. This includes Zoom credentials, social media login options, and SSO.
We require all users to log in to Zoom with their G Suite account. This provides the benefit of ensuring all Zoom accounts are protected by the same security controls that protect our Equal Experts accounts – including Two Factor Authentication.
It’s important to remember that user accounts aren’t automatically logged out or deleted from Zoom when the G Suite user is removed. It’s important to have a robust offboarding process in place to handle this.
Zoom’s attitude towards security
Perhaps the most subjective of all concerns is Zoom’s attitude towards security. We created this document to focus on facts, but this is a more complex topic to cover. Rather than voicing what can only be a subjective opinion, we think it’s best for each person to come to their own personal conclusions on this. We encourage you to consider the prime directive when forming your opinion, and do read the statement from Eric Yuan, Zoom CEO.
How we’re using Zoom
We’ve specifically set our account-level configuration options to address the risk introduced by the security issues described above. In doing so, we’ve tried to balance usability and security as best we can within the constraints of the product, but will revisit these options if we discover they are either too strong or too weak. We value feedback from our users on how well we’re striking this balance.
We do not compel individuals to use Zoom to host meetings. Through our use of G Suite, all users have access to Google Hangouts, which is another excellent option for video conferencing.
As with all products provided by Equal Experts to employees and associates, there is a shared responsibility between the company and the user. We pride ourselves on being a company of adults, and we have done our best to limit our use of more restrictive controls. We trust that each individual will consider their own account settings and set them appropriately – much like you might do when securing your Facebook or LinkedIn account.
Zoom with Clients
As a consultancy, we have to consider a slightly different set of scenarios compared to organisations that only use Zoom internally. We have our own internal business needs, as well as our clients’ business needs to consider.
Our business needs include interviews, internal meetings, sales, webinars, training, and other similar situations. We’re comfortable with our Zoom account being used for these purposes.
When working with clients, we follow their information security policies over our own. We prefer clients to provide the tools for storing or processing their data, rather than using our internal tools for this purpose. This ensures that the client is always in control of their data and able to configure their tools according to their policies. This often includes integration with other systems they use, such as IAM directories, Slack teams, and source control and issue tracking systems. Where the client does not have these systems in place, our preference is always to help them create their own accounts rather than use our internal systems.
To reiterate a point I made at the beginning of this article, our view on Zoom (and all other tools we use) is informed first and foremost by our threat model. It’s critically important that we avoid knee-jerk reactions to the news, but instead focus our efforts on validating the seriousness of the issues against our own circumstances. We continue to make informed decisions based not just on evidence, but on the application of that evidence to our context.
Learn more
If you want to learn some of the techniques we use to build high-performing remote-first teams watch this webinar.